Articles, News and Industry Tips
Read the latest articles on best practices, building customer-centric products, and the latest in cybersecurity.
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.

Cloud Security
CIS Controls v8 Explained: 18 Controls Every Organization Needs
April 10, 2026
CIS Controls v8 Explained: 18 Controls Every Organization Needs
Cloud Security
Cloud-Native Services Threat Modeling: STRIDE Framework, Controls & Automation
April 9, 2026
Cloud-Native Services Threat Modeling: STRIDE Framework, Controls & Automation

Software Supply Chain Security
Axios NPM Supply Chain Attack: Technical Analysis, IOCs, Detection & Mitigation
April 8, 2026
Axios NPM Supply Chain Attack: Technical Analysis, IOCs, Detection & Mitigation
Cloud Security
MCSB Deep Dive: Securing Azure with Microsoft Cloud Security Benchmark
April 6, 2026
MCSB Deep Dive: Securing Azure with Microsoft Cloud Security Benchmark

Vulnerability Management
Vulnerability Management Tools and Process: A Practitioner's Guide to Staying Ahead of Threats
April 6, 2026
Vulnerability Management Tools and Process: A Practitioner's Guide to Staying Ahead of Threats

Threat Integrations
Wiz Cloud Security: Everything You Need to Know About the Platform Securing the Modern Cloud
April 3, 2026
Wiz Cloud Security: Everything You Need to Know About the Platform Securing the Modern Cloud

Cloud Security
Security Controls in Cybersecurity: A Complete Guide to MCSB, CIS, and NIST Frameworks
March 24, 2026
Security Controls in Cybersecurity: A Complete Guide to MCSB, CIS, and NIST Frameworks
Artificial Intelligence (AI)
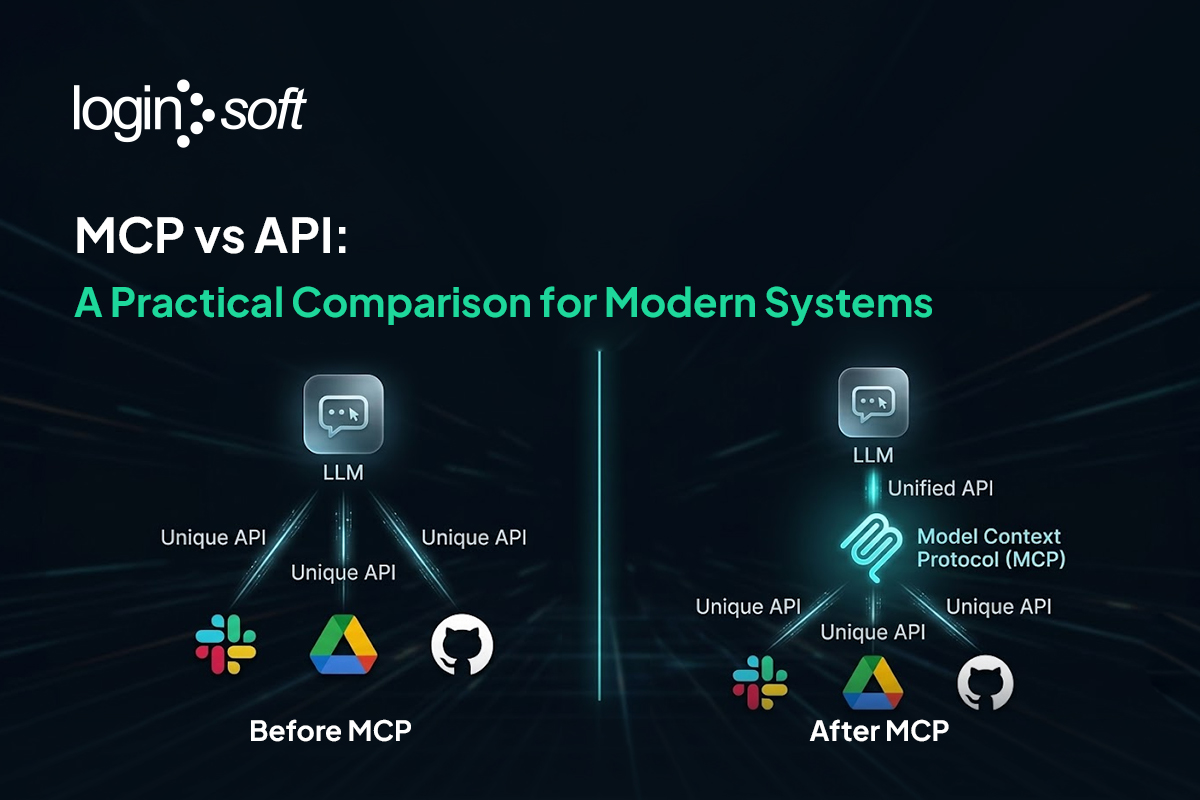
MCP vs API: What's the Actual Difference and When to Use Each
March 23, 2026
MCP vs API: What's the Actual Difference and When to Use Each

Cloud Security
Infrastructure Intelligence in Cybersecurity: Detect Threats Before They Launch
February 24, 2026
Infrastructure Intelligence in Cybersecurity: Detect Threats Before They Launch

Information Security
Microsoft Purview for Data Governance, Compliance & Risk Management
February 23, 2026
Microsoft Purview for Data Governance, Compliance & Risk Management

Artificial Intelligence (AI)
Claude Opus 4.6 Discovers 500+ Critical Vulnerabilities in Open-Source Software: What This Means for Cybersecurity
February 10, 2026
Claude Opus 4.6 Discovers 500+ Critical Vulnerabilities in Open-Source Software: What This Means for Cybersecurity

Threat Integrations
The Hidden Tax on Cybersecurity Integrations: Why Security Product Integrations Are Harder Than They Should Be and How Loginsoft Helps
January 19, 2026
The Hidden Tax on Cybersecurity Integrations: Why Security Product Integrations Are Harder Than They Should Be and How Loginsoft Helps









