Introduction
Every organization moving to the cloud faces a deceptively simple challenge: keeping cloud environments configured securely as they grow, change, and scale. In a world where a single misconfigured storage bucket or an overly permissive IAM role can expose millions of records, periodic security audits are no longer enough.
Cloud Security Posture Management (CSPM) has emerged as the essential capability that bridges this gap. CSPM continuously monitors your cloud infrastructure - across AWS, Azure, GCP, and hybrid environments - to detect misconfigurations, enforce compliance frameworks, and remediate risks before they become breaches. It is the security practice that answers the question every CISO needs answered in real time: “Is our cloud configured securely, and where are we exposed?”
In this guide, we break down what CSPM is, how it works, why it matters more than ever, and the specific capabilities your organization should demand from any CSPM solution. Whether you are evaluating your first CSPM tool or optimizing an existing deployment, this article provides the actionable framework you need to make informed decisions about protecting your cloud posture.
Key Takeaways
What You Will Learn from This Guide
1. Misconfigurations are your biggest cloud threat
Industry data shows that roughly 80% of organizations experienced a cloud breach in the past year, with human-caused misconfigurations driving the vast majority of incidents. CSPM catches these before attackers do.
2. Continuous monitoring replaces periodic audits
Cloud environments change constantly. CSPM provides real-time visibility and automated detection of insecure configurations not the outdated model of quarterly security reviews.
3. One security baseline, every cloud
Whether you operate on AWS, Azure, GCP, or all three, CSPM enforces a uniform security posture model that maintains a single consistent standard and automates compliance across your entire footprint.
What Is Cloud Security Posture Management (CSPM)?
Cloud Security Posture Management (CSPM) is a security practice and technology that continuously monitors cloud environments to identify, assess, and remediate misconfigurations, insecure settings, and compliance violations. Rather than relying on periodic manual reviews, CSPM tools connect directly to cloud provider APIs across Amazon Web Services, Microsoft Azure, Google Cloud Platform, and hybrid infrastructure to provide agentless, real-time visibility into how every resource is configured.
In simple terms, CSPM answers one critical question:
“Is our cloud configured securely, and where are we exposed?”
CSPM solutions work by automatically discovering all cloud assets (compute instances, storage buckets, databases, networking rules, IAM policies, serverless functions, and container orchestration configurations), then evaluating each against established security baselines, regulatory frameworks, and organizational policies. When deviations are found, CSPM generates prioritized alerts and, in many cases, can trigger automated remediation to fix the issue before it becomes an incident.
The scope of CSPM extends across Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and increasingly Software as a Service (SaaS) environment. As organizations adopt multi-cloud and hybrid strategies, CSPM provides the centralized visibility and control that manual configuration management simply cannot deliver at scale.
Why CSPM Is Non-Negotiable: The Business Case
The case for CSPM is driven by three converging realities that make it indispensable for any organization operating in the cloud.
Cloud Environments Change Constantly
Cloud infrastructure is dynamic by design. Developers spin up and tear down resources continuously, auto-scaling policies create and destroy instances in seconds, and infrastructure-as-code pipelines deploy changes multiple times per day. In this environment, a secure configuration today can become an exposed vulnerability tomorrow through routine operational changes, configuration drift, or a single accidental permission change. Periodic security audits conducted quarterly or even monthly leave dangerous gaps. CSPM fills this gap by providing continuous visibility and validation - not periodic checks - ensuring that every configuration change is evaluated against your security baseline in real time.
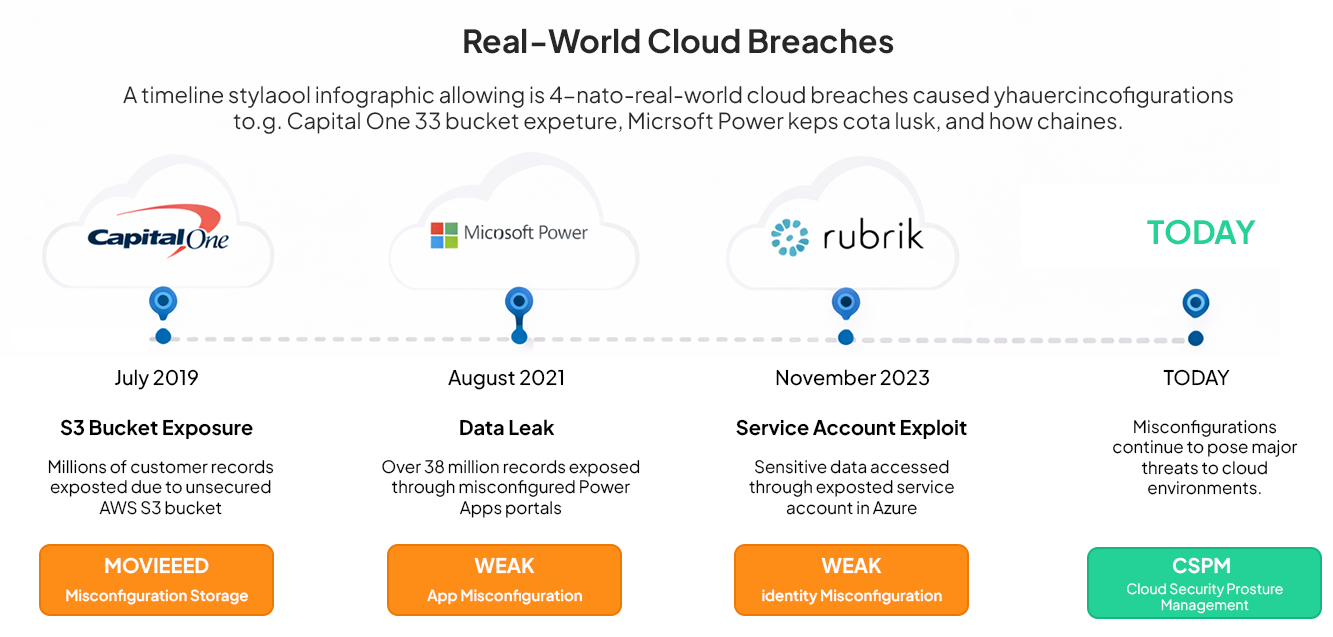
Misconfigurations Are the #1 Cause of Cloud Breaches
Industry research consistently confirms that misconfigured cloud resources - not sophisticated zero-day exploits - are responsible for the majority of cloud security incidents. Publicly accessible storage buckets, overly permissive IAM roles, unencrypted databases, and misconfigured network security groups create the openings that attackers exploit. The average cost of a data breach now runs into the millions, with organizations that detect breaches faster saving significantly compared to those with slower response times. CSPM directly addresses this by automating the detection of insecure configurations before they are exploited, providing early detection that prevents exposure from turning into incidents.
Security Must Scale Without Proportionally Increasing Headcount
Cloud adoption is accelerating, but security team budgets and hiring are not keeping pace. Organizations need a way to enforce security policies across thousands of cloud resources, hundreds of accounts, and multiple cloud providers without requiring a proportional increase in security analysts. CSPM provides the automation to scale security without increasing headcount, enforcing guardrails aligned with approved architectures and maintaining one consistent security baseline across the organization.

Essential CSPM Capabilities Your Organization Needs
Not all CSPM solutions are created equally. The following capabilities represent the core functionality that an effective CSPM implementation must deliver to protect your cloud environments.
Continuous Cloud Asset Discovery and Visibility
Your CSPM must automatically discover and maintain a real-time inventory of every cloud resource across all accounts, subscriptions, projects, and regions. This includes computing instances, storage, databases, serverless functions, container workloads, networking components, and IAM configurations. As new deployments and connections are implemented, the CSPM tool should automatically detect them and assess their security posture. Without complete visibility, security gaps are invisible.
Automated Misconfiguration Detection and Remediation
The core value of CSPM lies in continuously comparing current cloud configurations against predefined security policies, industry benchmarks (CIS, NIST, FSBP), and organizational standards. When deviations are detected, the system must generate prioritized alerts with step-by-step remediation guidance - and ideally support automated remediation workflows that fix common misconfigurations without human intervention. This automated detection of insecure configurations before they are exploited is what separates proactive security from reactive incident response.
Continuous Compliance Monitoring with Real-Time Evidence
Compliance is not a periodic exercise - it must be embedded into daily posture management. Your CSPM should continuously evaluate configurations against regulatory frameworks (PCI DSS, HIPAA, SOC 2, GDPR, ISO 27001) and generate audit-ready evidence in real time. This continuous compliance monitoring with real-time evidence eliminates the scramble of point-in-time assessments and ensures your organization always maintains audit readiness.
Identity Posture and Access Exposure Monitoring
In cloud environments, identity is the new perimeter. CSPM must provide continuous monitoring of identity posture and access exposure, identifying overprivileged accounts, dormant credentials, excessive cross-account access, and IAM policy violations. When combined with Cloud Infrastructure Entitlement Management (CIEM) capabilities, this analysis reveals the identity-based attack paths that traditional network-focused security tools miss entirely.
Uniform Security Posture Across Multi-Cloud Environments
Organizations operating across AWS, Azure, and GCP need a uniform security posture model across clouds. Your CSPM must normalize security findings across different cloud providers into a single, consistent baseline - ensuring that the same security standards and policies are enforced regardless of where workloads run. This prevents the fragmentation that occurs when each cloud team operates with its own security tools and definitions.
Contextual Risk Prioritization and Attack Path Analysis
Modern CSPM must go beyond simple rule-checking to evaluate whether a misconfiguration actually creates exploitable risk. Using graph-based analysis, advanced CSPM tools map resources as interconnected nodes, revealing attack paths that flat lists of findings miss entirely. By correlating factors like external exposure, data sensitivity, identity permissions, and existing vulnerabilities, CSPM surfaces only the issues that represent genuine risk - preventing alert fatigue and ensuring security teams focus on what truly matters.

How CSPM Works: The Four Continuous Phases
Understanding the mechanics of CSPM is essential to appreciate its role in cloud security. While each CSPM vendor implements these phases differently, the fundamental workflow follows four stages that operate continuously and concurrently.
The first phase is Asset Discovery. CSPM tools connect to cloud provider APIs using agentless connectivity to discover all cloud assets, services, and their interconnections. This creates a comprehensive, continuously updated inventory that forms the foundation for all subsequent security analysis.
The second phase is Configuration Assessment. Every discovered resource is evaluated against compliance standards, security benchmarks, and organizational policies. The system identifies which resources are configured in compliance and which deviate from established baselines, flagging specific misconfigurations with detailed context.
The third phase is Risk Prioritization. Not every misconfiguration carries equal risk. Modern CSPM tools score and prioritize findings by analyzing business context: Is the resource externally exposed? Does it contain sensitive data? Are the associated identity permissions excessive? Could an attacker chain multiple misconfigurations into a viable attack path? This contextual analysis transforms a raw list of findings into an actionable risk-ranked queue.
The fourth phase is Remediation and Prevention. Prioritized findings are routed to automated workflows, ticketing systems, or DevOps pipelines for resolution. For common misconfigurations, CSPM can automatically enforce the correct configuration. For complex issues, it provides detailed remediation guidance and integrates with infrastructure-as-code tools to prevent the same issue from being reintroduced.

CSPM vs. Related Cloud Security Technologies
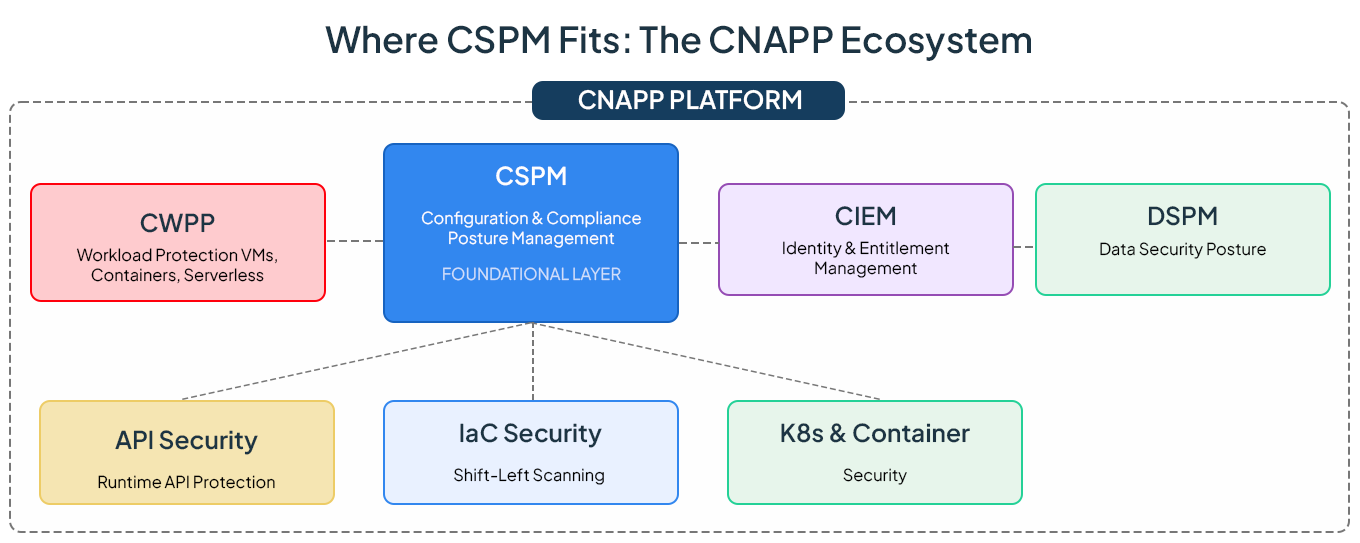
CSPM operates within a broader ecosystem of cloud security technologies. Understanding how these tools relate helps organizations build a comprehensive security architecture.
The industry is converging toward Cloud-Native Application Protection Platforms (CNAPPs) that unify CSPM, CWPP, CIEM, and DSPM into a single platform. Industry analysts have noted that the majority of new CSPM purchases are now made as part of integrated CNAPP offerings, reflecting the demand for consolidated cloud security that eliminates tool sprawl and provides holistic visibility.
Implementing CSPM: A Step-by-Step Approach
Successful CSPM implementation follows a methodical approach that begins with visibility and progress through enforcement and continuous improvement.
Step 1: Inventory your cloud assets
Establish complete visibility into your cloud estate by connecting your CSPM to every cloud account, subscription, and project. The tool will automatically discover computers, storage, networking, identity, and serverless resources across all regions.
Step 2: Define your security baseline and compliance requirements
Map your regulatory obligations and industry benchmarks to specific configuration rules. This becomes the policy framework your CSPM will enforce - frameworks like CIS Benchmarks, NIST 800-53, PCI DSS, HIPAA, SOC 2, and GDPR are commonly adopted starting points.
Step 3: Enable continuous monitoring and configuration assessment
Activate real-time monitoring so that every configuration change is evaluated as it happens. This catches insecure settings, open storage, excessive permissions, and compliance drift immediately.
Step 4: Prioritize risks using contextual analysis
Configure your CSPM to score findings based on business context - data sensitivity, network exposure, identity permissions, and exploitability. This prevents alert fatigue and focuses effort on genuine attack paths.
Step 5: Automate remediation and enforce guardrails
Set up automated workflows for common misconfigurations. Integrate CSPM with CI/CD pipelines and infrastructure-as-code tools to enforce preventive guardrails aligned with approved architectures, blocking insecure configurations before deployment.
Step 6: Measure, report, and continuously improve
Track your security posture score over time, generate compliance reports, and benchmark improvements. Refine policies as your architecture evolves, and new threats emerge.

The Strategic Value of CSPM for Your Organization
The return on CSPM investment extends beyond preventing breaches. Organizations with mature CSPM implementations realize value across multiple dimensions. CSPM prevents avoidable cloud risks by catching misconfigurations before they become incidents, directly reducing the probability and potential cost of data breaches. It protects revenue and brands by ensuring that customer data, intellectual property, and business-critical systems are not exposed through preventable configuration errors. CSPM provides continuous compliance monitoring that reduces audit preparation time from weeks to hours, with real-time evidence generation that keeps the organization perpetually audit ready. And by automating detection, prioritization, and remediation, CSPM enables security teams to manage increasingly complex cloud environments without proportionally increasing headcount.
As cloud environments grow more complex and the threat landscape continues to evolve, CSPM is no longer a nice-to-have capability it is the foundational security practice that determines whether your cloud operates as a secure, compliant business asset or an unmanaged risk surface.

FAQs
Q1: What is Cloud Security Posture Management (CSPM)?
Cloud Security Posture Management (CSPM) is a security practice and technology that continuously monitors cloud environments to identify, assess, and remediate misconfigurations, insecure settings, and compliance violations across IaaS, PaaS, and SaaS services. In simple terms, CSPM answers the question: "Is our cloud configured securely, and where are we exposed?"
Q2: Why is CSPM important for cloud security?
CSPM is critical because cloud misconfigurations are the number one cause of cloud breaches. Industry analysts estimate that the vast majority of cloud security incidents stem from customer-side misconfigurations rather than provider vulnerabilities. CSPM provides automated, continuous monitoring to catch these misconfigurations before attackers can exploit them, directly reducing breach risk and associated costs.
Q3: What is the difference between CSPM and CNAPP?
CSPM focuses specifically on monitoring and remediating cloud infrastructure configurations and compliance. CNAPP (Cloud-Native Application Protection Platform) is a broader unified platform that combines CSPM with Cloud Workload Protection (CWPP), Cloud Infrastructure Entitlement Management (CIEM), Data Security Posture Management (DSPM), API security, container security, and more. The industry trend is toward CNAPP adoption, with most new CSPM purchases now made as part of integrated CNAPP offerings.
Q4: How does CSPM work?
CSPM tools connect to cloud provider APIs using agentless connectivity to continuously perform four key phases: (1) discover all cloud assets across accounts and regions, (2) assess configurations against security baselines and compliance frameworks, (3) prioritize risks based on business context, exploitability, and attack path analysis, and (4) automate remediation workflows or provide step-by-step guidance for resolution.
Q5: What is Cloud-Native Services Threat Modeling?
Cloud-native services threat modeling is the practice of systematically identifying, assessing, and mitigating security threats specific to cloud-native architectures - including serverless functions, containers, Kubernetes clusters, managed databases, and API gateways. It evaluates how cloud services interact and where misconfigurations or design flaws could create exploitable attack paths. CSPM provides the foundational configuration data that makes effective cloud-native threat modeling possible.
Q6: Can CSPM work across multiple cloud providers?
Yes. Modern CSPM solutions are designed for multi-cloud and hybrid environments, providing a unified security baseline and consistent compliance monitoring across AWS, Microsoft Azure, Google Cloud Platform, and on-premises infrastructure. This uniform posture model ensures that security policies are enforced consistently regardless of where workloads run.
Q7: What compliance frameworks does CSPM support?
CSPM solutions typically support NIST 800-53, PCI DSS, HIPAA, SOC 2, ISO 27001, CIS Benchmarks, GDPR, and cloud-specific benchmarks like AWS Foundational Security Best Practices and the Microsoft Cloud Security Benchmark. The specific frameworks vary by vendor, so evaluate against your organization's regulatory obligations.
Q8: How does CSPM reduce alert fatigue?
Modern CSPM tools use graph-based analysis and contextual risk scoring to prioritize alerts based on actual exploitability and business impact, rather than flagging every deviation equally. By correlating factors like network exposure, data sensitivity, identity permissions, and existing vulnerabilities, CSPM surfaces only the small percentage of issues that represent genuine attack paths - helping security teams focus on what truly matters.
Get Notified
BLOGS AND RESOURCES