Introduction
For every CISO, CTO, or board-level executive responsible for enterprise risk, one question keeps recurring: “Are we doing the right things, in the right order, to stop the attacks that actually matter?”
The CIS Critical Security Controls answered that question. Maintained by the Center for Internet Security and grounded in real-world attack data from MITRE ATT&CK and the Verizon DBIR, these 18 controls are the industry’s most pragmatic, evidence-based blueprint for cyber defense. The latest release CIS Controls v8.1 (June 2024) adds NIST CSF 2.0 alignment, a new Govern security function, and 153 measurable safeguards designed for cloud, hybrid, and remote-first environments.
In this guide, Loginsoft breaks down all 18 controls, explains the Implementation Group model, and provides a roadmap for operationalizing the framework whether you are building foundational hygiene or validating advanced defenses.
Key Takeaways
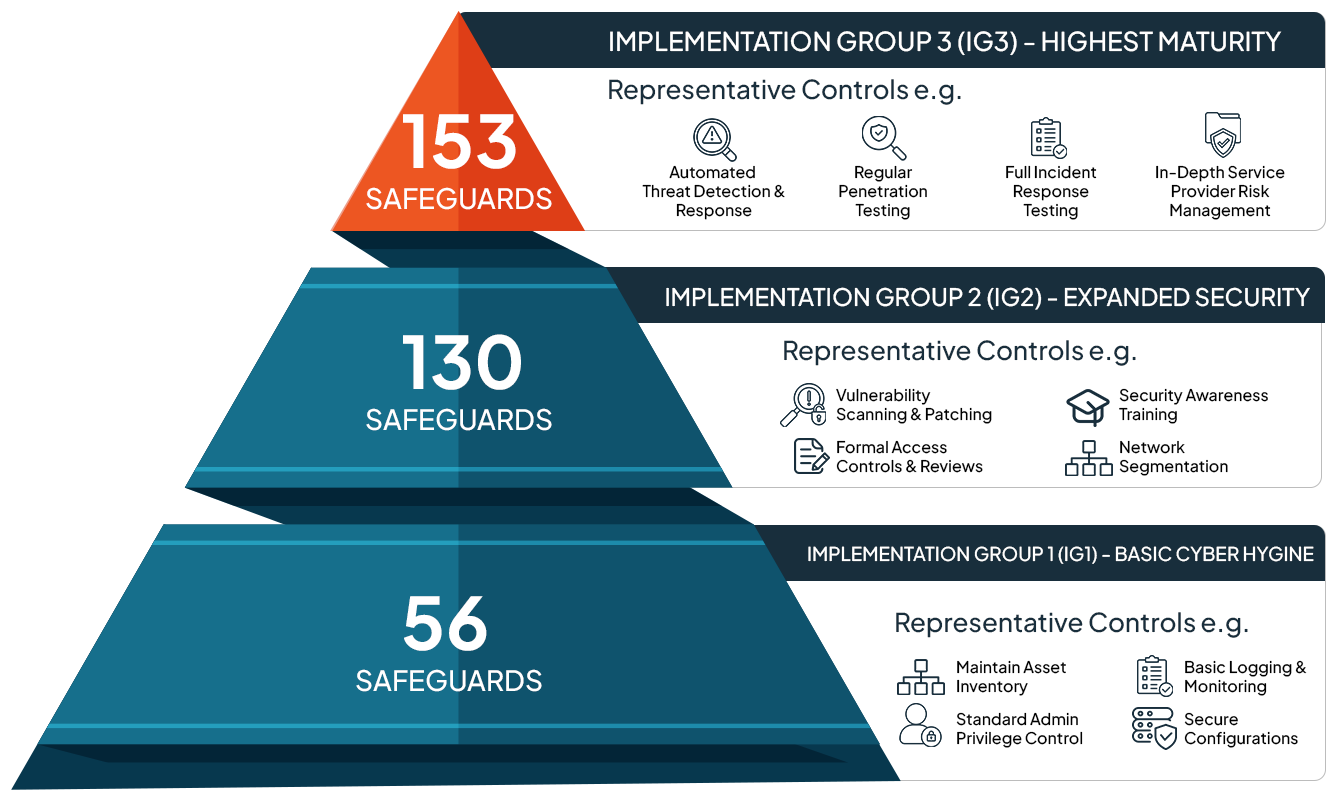
- CIS Controls v8.1 organizes 153 safeguards across 18 controls, and three Implementation Groups start with IG1’s 56 essential safeguards to defend against the most common attacks.
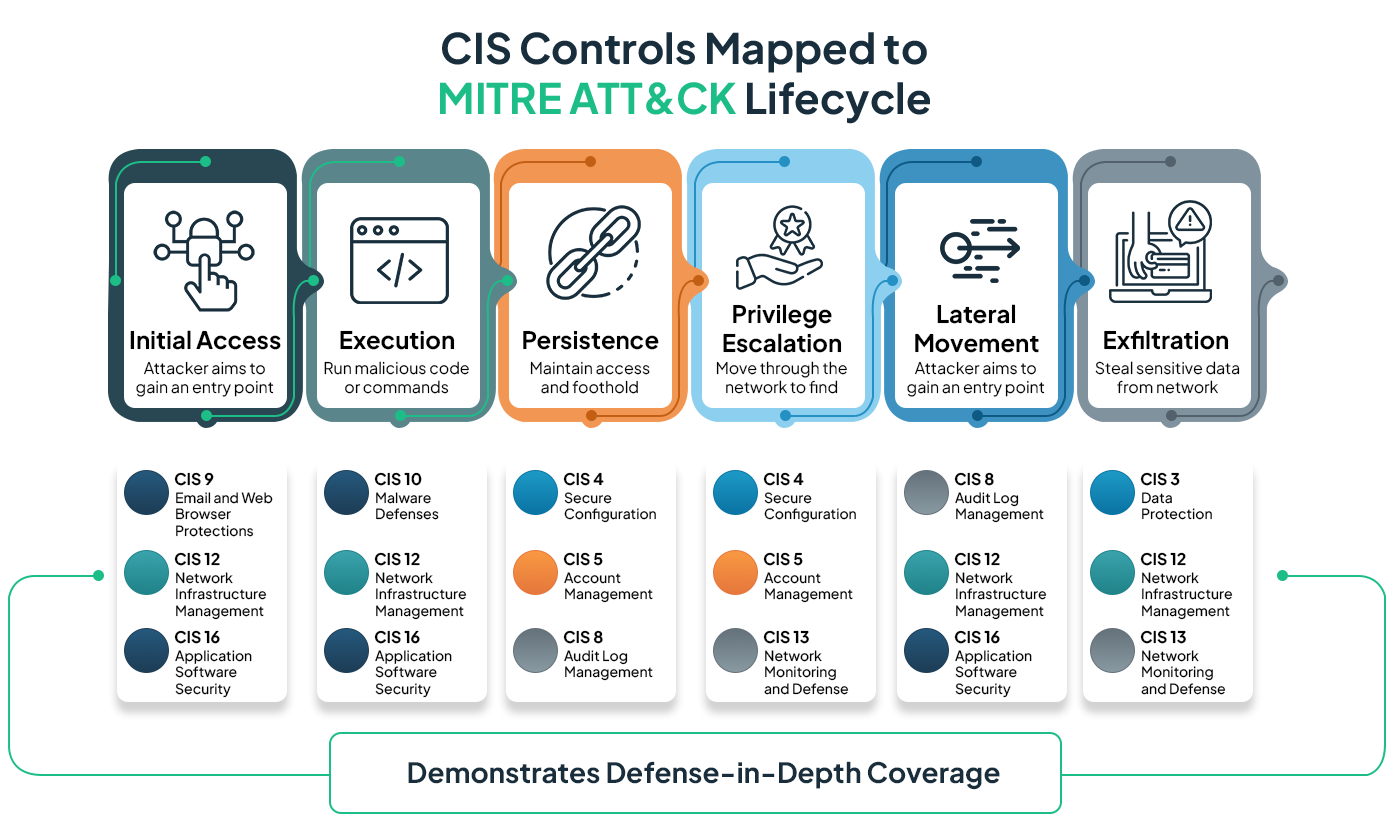
- Full CIS Controls implementation defends against 86% of MITRE ATT&CK techniques (91% for the top five attack types), making it one of the highest-ROI cybersecurity frameworks available.
- Version 8.1 adds a Govern security function aligned to NIST CSF 2.0, enabling CXOs to map a single implementation effort across multiple regulatory requirements simultaneously.
What Are the CIS Critical Security Controls?
Originally developed in 2008 as the SANS Top 20 Critical Security Controls, the framework has been curated for nearly two decades based on real-world attack intelligence. The Center for Internet Security assumed stewardship in 2015, and the controls have since evolved through multiple versions to keep pace with how organizations operate and how adversaries attack.
At their core, the CIS Controls are a prioritized, prescriptive set of cybersecurity best practices.
"Unlike broader governance frameworks that describe what to protect, the CIS Controls tell you how with specific, measurable safeguards organized in the order that delivers the most defensive value per unit of effort. Each safeguard is mapped to the MITRE ATT&CK framework, which means every recommendation is traceable to actual attacker behavior observed in the wild. "
Version 8 reduced the control count from 20 to 18 by reorganizing activities rather than device ownership. This shift acknowledges that in a cloud-first, hybrid-workforce environment, the question is no longer “who manages this device?” but “what defensive activity needs to happen, regardless of where the asset lives?”
v8.1 Update (June 2024): Added 25 new “Govern” function safeguards aligned to NIST CSF 2.0, introduced a Documentation asset class (plans, policies, procedures), revised asset class mappings, and enhanced glossary definitions for clearer implementation. The total safeguard count is now 153.
All 18 CIS Controls Explained
Below is a CXO-level overview of every control. Each description focuses on the strategic intent of the “why these matters to your business” alongside the technical scope. Implementation Group applicability is indicated so you can immediately assess relevance to your current maturity tier.
Controls 1-6, Know Your Environment
1. Inventory and Control of Enterprise Assets
You cannot protect what you do not know exists. This control requires actively managing all enterprise assets - endpoints, servers, IoT devices, cloud instances, and virtual machines - connected to your infrastructure physically, virtually, or remotely. The goal is an authoritative, continuously updated inventory that identifies unauthorized and unmanaged assets before attackers exploit them.
2. Inventory and Control of Software Assets
Shadow IT and unapproved software are leading initial access vectors. This control mandates tracking every operating system and application on your network to ensure only authorized software executes. Unauthorized or unmanaged software must be identified and either removed or blocked from installation.
3. Data Protection
Data is the asset adversaries ultimately target. This control establishes processes and technical controls to identify, classify, securely handle, retain, and dispose of data across its lifecycle. In an era of ransomware double-extortion and regulatory data-residency requirements, classification and handling are no longer optional.
4. Secure Configuration of Enterprise Assets and Software
Default configurations are designed for ease of deployment, not security. This control requires establishing and maintaining hardened configurations for endpoints, network devices, IoT systems, servers, and software. CIS Benchmarks provide vendor-neutral, consensus-based configuration guides for hundreds of platforms-and this control operationalizes them.
5. Account Management
Credential compromise remains the top attack vector across nearly every industry. This control addresses the lifecycle management of user accounts, administrator accounts, and service accounts, from provisioning through deactivation, ensuring that stale, orphaned, or overprivileged credentials do not become entry points.
6. Access Control Management
Beyond account existence, this control governs the privileges attached to those accounts. It mandates processes and tooling to create, assign, manage, and revoke access credentials based on the principle of least privilege. Version 8.1 added Govern safeguards specifically requiring documented role-based access policies and regular privilege reviews.
7. Continuous Vulnerability Management
Vulnerabilities are disclosed daily; your adversaries triage them just as fast. This control calls for a continuous process not an annual scan to assess, track, and remediate vulnerabilities across all enterprise assets, minimizing the exposure window. It also requires monitoring public and private threat intelligence sources for emerging vulnerability and exploit information.
8. Audit Log Management
Logs are the forensic record of everything that happens in your environment. This control requires collecting, alerting on, reviewing, and retaining audit logs sufficient to detect, understand, and recover from a security incident. Without disciplined log management, incident response teams operate blind.
9. Email and Web Browser Protections
Phishing and malicious web content remain the most effective initial compromise techniques. This control targets improving protections and detections across email and browser vectors the two channels where attackers directly manipulate human behavior through social engineering, malicious links, and weaponized attachments.
10. Malware Defenses
Despite advances in attacker tradecraft, malware remains a core component of most intrusions. This control addresses preventing or controlling the installation, spread, and execution of malicious code, scripts, and applications across enterprise assets through endpoint protection, behavioral analysis, and file integrity mechanisms.
11. Data Recovery
Ransomware has made backup strategy a board-level topic. This control mandates establishing and maintaining data recovery practices sufficient to restore enterprise assets to a pre-incident, trusted state. That includes tested backup procedures, isolated or immutable backup storage, and defined recovery time objectives that align with business continuity requirements.
12. Network Infrastructure Management
Misconfigured network devices are silent vulnerabilities. This control covers the active management of routers, switches, firewalls, and other network infrastructure to prevent attackers from exploiting vulnerable services and access points. It includes ensuring up-to-date firmware, removing default credentials, and segmenting network traffic appropriately.
Controls 13-18 - Monitor, Respond, and Validate
13. Network Monitoring and Defense
Perimeter defense alone is insufficient; you need visibility into lateral movement and anomalous traffic patterns. This control establishes processes and tooling for comprehensive network monitoring and defense against threats across the enterprise’s network infrastructure and user base, including east-west traffic inspection.
14. Security Awareness and Skills Training
Technology controls are undermined by untrained users. This control requires a sustained security awareness program that influences workforce behavior, builds practical security skills, and reduces human-error risk. The emphasis is on measurable behavior change, not check-the-box annual training modules.
15. Service Provider Management
Your supply chain is your attack surface. This control establishes a process to evaluate and continuously monitor service providers who hold sensitive data or manage critical IT platforms, ensuring third-party risk does not undermine your internal controls. In the age of SaaS-dependency and third-party breaches, this is a C-suite imperative.
16. Application Software Security
Applications-whether developed in-house, acquired, or hosted - are a primary attack surface. This control addresses the full security lifecycle of application software: preventing, detecting, and remediating weaknesses before they can be exploited. It covers secure SDLC practices, dependency scanning, and runtime protections.
17. Incident Response Management
When a breach occurs - and one eventually will - response speed determines the magnitude of damage. This control mandates a formal incident response program with defined roles, documented procedures, regular exercises, and clear communication plans. The goal is preparation, detection, containment, and rapid recovery.
18. Penetration Testing
Trust but verify. This control requires testing the effectiveness of your controls through simulated attacks that identify and exploit weaknesses in people, processes, and technology. Penetration testing validates that the other 17 controls are working as intended and reveals gaps that assessments alone cannot surface.
Implementation Groups: A Tiered Approach to Maturity
Not every organization needs all 153 safeguards on day one. CIS designed Implementation Groups as a practical on-ramp, allowing your enterprise to self-assess its risk profile and resource availability, then focus on the safeguards that deliver the most defensive value at your current maturity level.
Executive Insight: IG1 is not a “beginner tier”-it is the minimum standard of information security that every enterprise should implement. If your organization has not completed IG1, that should be the immediate priority regardless of size or industry. Everything else builds from that foundation.
Why CIS Controls v8 Should Be on Every CXO’s Agenda
Cross-framework compliance efficiency
CIS Controls v8.1 maps to NIST CSF 2.0, HIPAA, PCI DSS, SOC 2, CMMC, and ISO 27001. A single implementation effort yields compliance evidence across multiple regulatory obligations, reducing audit fatigue and duplicated work for your security team.
Evidence-based prioritization
Unlike frameworks that leave prioritization to interpretation, CIS Controls rank safeguards by demonstrated defensive value against observed attack patterns. The Community Defense Model validates each control against real-world breach data, giving CXOs confidence that resources are allocated to the activities that reduce the most risk.
Scalability without complexity
The Implementation Group model means a 50-person company and a 50,000-employee enterprise can both use the same framework-starting at the same IG1 baseline and extending to different depths based on risk tolerance and capability.
Board-ready governance
The new Govern function in v8.1 produces the documented policies, procedures, and accountability structures that boards and regulators expect to see, bridging the gap between technical controls and executive oversight.
How Loginsoft Accelerates CIS Controls Implementation
At Loginsoft, we have spent over 16 years engineering cybersecurity solutions for enterprises and security product companies alike. Our capabilities map directly to the operational demands of the CIS Controls framework.
Vulnerability Intelligence and Configuration Management
Our security advisory research generates metadata for vulnerabilities in open-source components, and our SCAP/OVAL content development supports vulnerability management, patch management, and compliance management aligned to Controls 4, 7, and 16. With over 500 CVEs discovered in open-source software, our vulnerability intelligence delivers the early-warning capability that Control 7 demands.
SIEM, SOAR, and TIP Integration Engineering
Controls 8 and 13 require robust log management and network monitoring. Loginsoft has delivered 250+ integrations across platforms like Splunk, Palo Alto, IBM Security, ThreatConnect, and Elastic, building connectors, playbooks, and dashboards that operationalize these controls at scale.
Cloud-Native Security
For organizations extending CIS Controls into cloud and hybrid environments, Loginsoft delivers CIS Benchmark-hardened container images, CSPM policy-as-code, and runtime workload protection aligned to Controls 1, 2, 4, and 12.
Continuous Security Monitoring
Our real-time monitoring solutions combine threat intelligence feeds, automated alerting, and vulnerability analysis to maintain the continuous visibility that the CIS framework requires-turning Controls 7, 8, and 13 from aspirational goals into operational reality.
FAQs
Q1. What are CIS Controls v8 and how many controls are there?
CIS Controls v8 is a prioritized set of 18 cybersecurity best practices maintained by the Center for Internet Security. The latest iteration, v8.1 (released June 2024), breaks these 18 controls into 153 individual safeguards. Each safeguard is specific, measurable, and mapped to the MITRE ATT&CK framework based on real-world threat intelligence. The framework is designed to be scalable for organizations of any size, from small businesses to Fortune 500 enterprises.
Q2. What is the difference between CIS Controls v7 and v8?
Version 8 consolidated the previous 20 controls down to 18 by reorganizing them around activities rather than device ownership. This shift directly addresses cloud, hybrid, and remote-work environments. The terminology changed from “Sub-Controls” to “Safeguards,” and Implementation Groups were refined to provide clearer prioritization guidance. Version 8.1 further enhanced the framework with NIST CSF 2.0 alignment and a new Govern security function.
Q3. What are Implementation Groups (IG1, IG2, IG3) in CIS Controls?
Implementation Groups are self-assessed tiers that help organizations prioritize safeguard adoption based on risk profile, size, and available resources. IG1 includes 56 essential safeguards that every organization should implement regardless of industry. IG2 adds 74 additional safeguards for organizations with moderate complexity and regulatory obligations. IG3 includes all 153 safeguards and is intended for enterprises facing sophisticated threats. The groups are cumulative: IG2 includes all of IG1, and IG3 includes everything.
Q4. How do CIS Controls map to NIST CSF 2.0 and other frameworks?
CIS Controls v8.1 includes official mappings to NIST CSF 2.0 security functions (Identify, Protect, Detect, Respond, Recover, and the new Govern function). The CIS also provides community-developed mapping documents for HIPAA, PCI DSS, SOC 2, ISO 27001, and CMMC. This allows organizations to implement CIS Controls and simultaneously generate compliance evidence for multiple regulatory frameworks.
Q5. How effective are CIS Controls at stopping real-world cyberattacks?
The CIS Community Defense Model, which analyzes controls effectiveness against MITRE ATT&CK techniques and Verizon DBIR data, found that implementing all CIS Controls defends against approximately 86% of ATT&CK techniques. Against the top five most common attack types, that effectiveness rises to 91%. Even IG1 alone provides substantial protection against the attack patterns most frequently observed in the wild.
Q6. Where should my organization start with CIS Controls implementation?
Start with Implementation Group 1. Within IG1, prioritize based on your current gaps. If you lack a complete asset inventory, begin with Controls 1 and 2. If your backup and recovery processes have not been tested, prioritize Control 11. Once IG1 is operational, conduct a gap assessment against IG2 safeguards and expand coverage based on your risk profile and regulatory requirements. CIS Controls implementation is an ongoing program, not a one-time project.
Q7. What changed in CIS Controls v8.1 compared to v8.0?
CIS Controls v8.1, released in June 2024, introduced 25 new Govern function safeguards aligned to the NIST CSF 2.0 governance requirements. It added a Documentation asset class covering plans, policies, and procedures, which had not been explicitly tracked in previous versions. Glossary definitions were expanded for terms like “plan,” “process,” and “sensitive data,” and Safeguard-to-asset mappings were revised for clearer implementation guidance.
Q8. How do CIS Controls help with regulatory compliance (HIPAA, PCI, SOC 2, CMMC)?
The CIS Controls are designed to create a strong security baseline that satisfies overlapping requirements across multiple regulatory frameworks. By implementing CIS Controls and using the official mapping documents provided by CIS, organizations can produce compliance evidence for HIPAA, PCI DSS, SOC 2, CMMC, ISO 27001, and NIST CSF simultaneously. This reduces audit preparation time and prevents duplicated security efforts across compliance programs.
Q9. Can CIS Controls be applied to cloud environments and hybrid infrastructure?
Yes. CIS Controls v8 was fundamentally redesigned to address cloud, hybrid, and remote-work environments. The activity-based control structure applies regardless of whether assets reside on-premises, in public cloud, in SaaS applications, or at employee home offices. CIS also publishes Cloud Companion Guides and platform-specific CIS Benchmarks for AWS, Azure, GCP, and major SaaS platforms to support cloud-native implementation.
Q10. How can Loginsoft help my organization implement CIS Controls?
Loginsoft provides cybersecurity engineering services that directly operationalize CIS Controls for enterprises. Our capabilities include vulnerability intelligence and SCAP/OVAL-based configuration management (Controls 4, 7, 16), SIEM/SOAR/TIP integration development with 250+ completed integrations (Controls 8, 13), CIS Benchmark-hardened container images and CSPM policy-as-code for cloud environments (Controls 1, 2, 4, 12), and continuous security monitoring with real-time threat intelligence (Controls 7, 8, 13). We work with organizations from gap assessment through continuous compliance operations.
Explore the key security, speed, and performance differences between TLS 1.3 and TLS 1.2
Ready to Find and Fix Your Security Weak Points?
LoginSoft's cybersecurity experts help organizations conduct thorough gap analyses, build prioritized remediation roadmaps, and achieve measurable security maturity improvements.
Schedule a Security Assessment
Hari Charan
A MESSAGE FROM OUR TECHNOLOGY LEADER
The NVD enrichment cutback is not a surprise to us - it’s the inflection point we’ve been preparing for. At Loginsoft, we’ve spent years building the research depth and tooling infrastructure to independently enrich vulnerabilities at scale, with the accuracy and context modern security programs require. LOVI is our answer. Our mission is simple: ensure that no CVE relevant to your environment goes unanalyzed, unscored, or unactioned - regardless of what remains in NIST’s queue.
Get Notified
BLOGS AND RESOURCES