Introduction: Why Your Security Controls May Not Be as Strong as You Think
Cyberattacks are no longer a matter of if but when. With threats evolving daily and regulatory scrutiny intensifying, the security controls that protected your organization last year may already have blind spots. The challenge is that most organizations don't know exactly where those blind spots are until a breach exposes them.
That is the problem a security controls gap analysis solves. Instead of waiting for an attacker to find the cracks in your defenses, a gap analysis gives you a structured, repeatable method for identifying weaknesses, measuring them against industry best practices, and building a prioritized plan to close them before they become incidents.
In this guide, we walk through everything you need to know what a security controls gap analysis actually involves, the step-by-step process for performing one, the frameworks professionals rely on, the most common gaps organizations discover, and how to turn findings into measurable security improvements. Whether you are preparing for a compliance audit, responding to a board-level security question, or simply strengthening your defenses, this guide will help you approach it with confidence.
Key Takeaways
1. A security controls gap analysis compares your current defenses to a recognized framework
(such as NIST CSF, ISO 27001, or CIS Controls) to pinpoint exactly where controls are missing, misconfigured, or underperforming-so you fix what matters instead of guessing.
2. The most dangerous gaps are rarely technical alone
Process failures, undocumented procedures, and unclear ownership cause recurring weaknesses that vulnerability scanners cannot detect. An effective gap analysis evaluates people, processes, and technology together.
3. Gap analysis is not a one-time event
it is a continuous improvement cycle. Organizations that reassess regularly, tie findings to risk-based remediation roadmaps, and track closure rates over time to build measurably stronger and more resilient security programs.
What Is a Security Controls Gap Analysis?
A security controls gap analysis is a structured assessment that compares an organization's existing security controls, policies, and processes against a defined target state - typically a recognized framework, regulatory standard, or internal security benchmark. The objective is straightforward: identify where controls are absent, partially implemented, or ineffective, and produce a prioritized action plan to address those deficiencies.
Think of it as a diagnostic health check for your entire security program. It goes well beyond what a vulnerability scanner can detect. While a scanner finds missing patches or open ports, a gap analysis evaluates the full spectrum of your security posture: governance practices, identity and access management, endpoint protection, cloud security configurations, data protection policies, incident response readiness, logging and monitoring effectiveness, and third-party risk management.
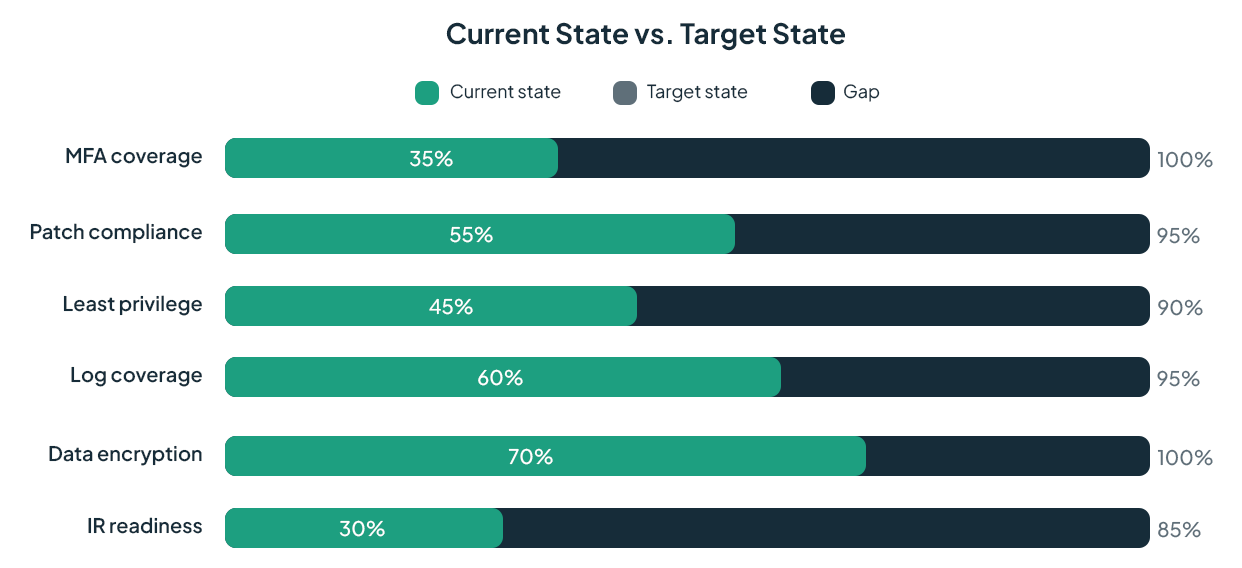
In practical terms: If a compliance framework requires multi-factor authentication on all privileged accounts but your environment only enforces MFA on email, the gap analysis flags that discrepancy, scores its risk, and places it on the remediation roadmap. It turns abstract "best practices" into concrete action items with owners, deadlines, and measurable outcomes.
The output is not just a list of problems it is a prioritized blueprint for improving security maturity. Organizations use it to prepare audits, justify security budgets, satisfy regulatory requirements, and make informed decisions about where to invest limited resources for maximum risk reduction.

Gap Analysis vs. Risk Assessment vs. Vulnerability Scan
These three activities are complementary but serve distinct purposes. Understanding the difference prevents wasted effort and ensures you are applying the right tool to the right problem.

The most effective security programs use all three. A vulnerability scan feeds technical data into the gap analysis, which is informed by the risk assessment's understanding of business context and threat landscape. Together, they produce a defense strategy that is both technically sound and aligned with organizational priorities.
Why a Security Controls Gap Analysis Matters Now
Several forces make gap analysis more critical today than it has ever been. The shift to hybrid and multi-cloud architectures has dramatically expanded attack surfaces. Remote workforces have introduced new endpoint and access management challenges. Regulatory frameworks from NIST CSF 2.0 to evolving data privacy laws-continue raising the bar for demonstrable control effectiveness.
Meanwhile, attackers are not waiting for organizations to catch up. According to Verizon's Data Breach Investigations Report, the majority of breaches involve the human element-exactly the kind of process and policy weakness that a technical scan alone cannot catch. Organizations that rely solely on automated scanning without evaluating the broader control environment are leaving significant risk unmanaged.
A well-executed gap analysis provides several concrete benefits: it reveals hidden weaknesses before attackers exploit them, creates a defensible view of your security posture for auditors and regulators, helps leadership make data-driven decisions about security investments, aligns security spending with actual risk rather than vendor hype, and establishes a measurable baseline for tracking improvement over time.
Choosing the Right Framework as Your Benchmark
Every gap analysis begins with selecting a target state-the standard against which your controls will be measured. The choice depends on your industry, regulatory obligations, customer requirements, and organizational maturity. Here are the frameworks most commonly used:

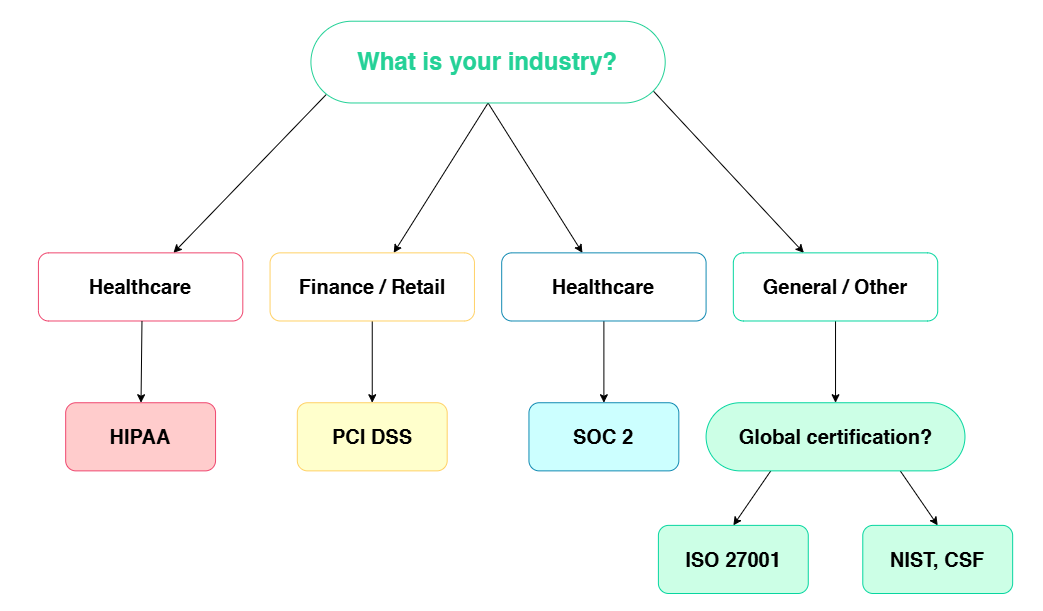
The framework you select becomes the measuring stick for the entire analysis. Organizations often need to satisfy multiple frameworks simultaneously in which case, a unified control mapping approach prevents redundant work and ensures comprehensive coverage.
How to Perform a Security Controls Gap Analysis: 7 Steps
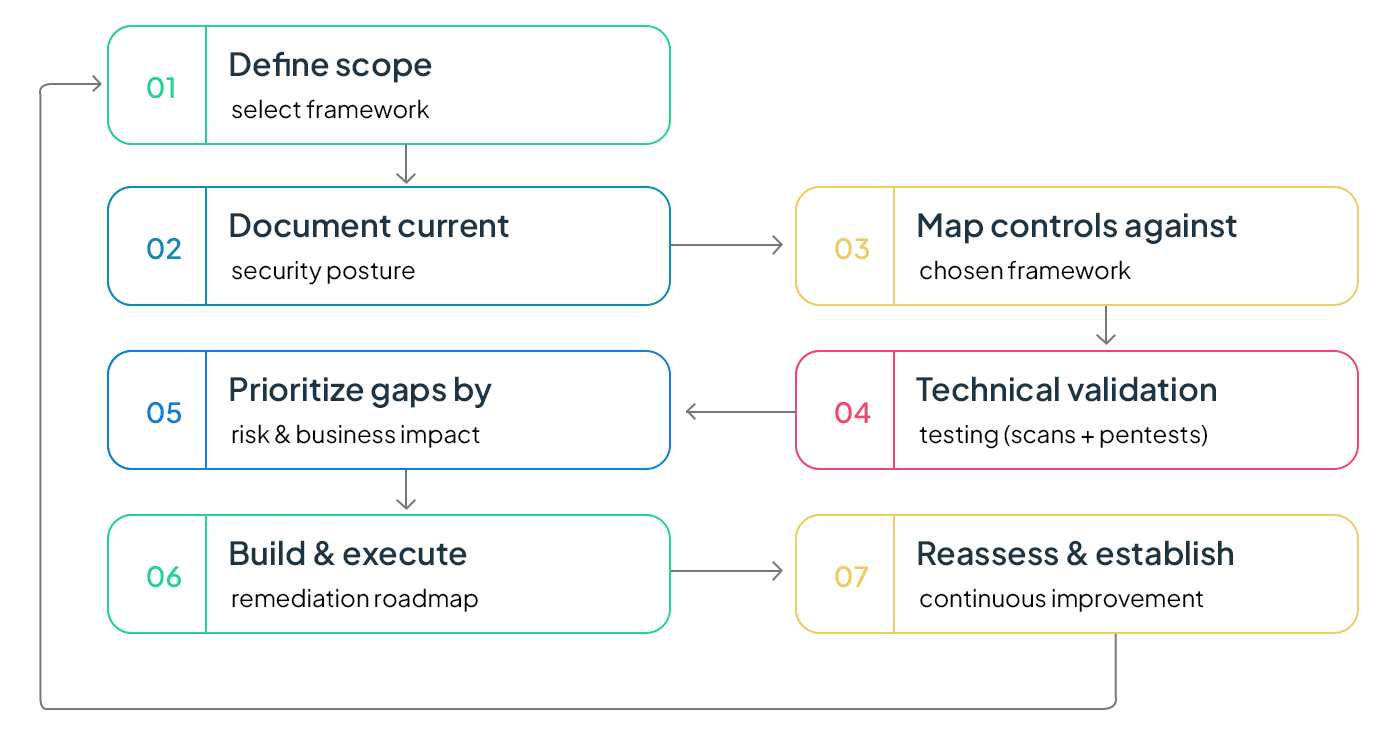
1. Define Scope and Select a Security Framework
Establish the boundaries of your analysis. Determine which systems, business units, data types, and third-party relationships are in scope. Then select the framework (NIST CSF, ISO 27001, CIS Controls, etc.) that aligns with your regulatory obligations and business requirements. This framework becomes the baseline against which every control is measured.
Scope definition is critical-too narrow and you miss important gaps; too broad and the project becomes unwieldy. Start with your most critical assets and highest-risk areas, then expand in subsequent cycles.
2. Document Your Current Security Posture
Build a comprehensive inventory of what you have today. This includes documenting all security controls across key domains: identity and access management (IAM), endpoint security, network security, cloud configurations, data protection, logging and monitoring, and incident response. Map data flows between systems, document how users authenticate and what permissions they hold, and gather all existing security policies and procedures.
Interview key personnel across IT, security, compliance, and operations. Frontline staff often have insights about how controls actually operate in practice versus how they are documented on paper. A control that exists in policy but is not consistently followed is functionally the same as a missing control.
3. Map Controls Against the Chosen Framework
Systematically compare each documented control against the requirements of your selected framework. For every control area, assess whether the control is fully implemented, partially implemented, or absent. Use a maturity scoring model-a 0-to-5 scale is common-to grade how effectively each control operates, not just whether it exists.
This step should evaluate both technical and process-level controls. If a patching tool is deployed but the patching process is inconsistent or undocumented, the weakness persists regardless of the technology. Assign a single accountable owner for each control area to prevent gaps in responsibility where everyone assumes someone else is managing it.
4. Conduct Technical Validation Testing
Augment the policy and process review with hands-on technical testing. Run vulnerability scans to identify missing patches, misconfigurations, and known security flaws. Perform penetration testing to simulate real-world attacks and determine whether identified gaps are actually exploitable. Review cloud environments for exposed storage buckets, over-permissioned service accounts, insecure API endpoints, and insufficient logging.
Assess your monitoring and detection capabilities: Are alerts actionable or buried in noise? Does your SIEM have coverage for major threat scenarios? Is log retention sufficient to support incident investigation? Detection gaps are often the most underweighted area in a gap analysis, yet they directly determine how quickly your team can identify and contain a breach.
5. Prioritize Gaps by Risk and Business Impact
Not every gap demands immediate attention. Evaluate each finding based on two dimensions: the likelihood that the gap will be exploited and the potential business impact if it is. Classify findings as high, medium, or low priority.
High-priority gaps-such as missing MFA on privileged accounts, unpatched critical vulnerabilities with active exploits, or absent encryption on sensitive customer data - require immediate remediation. Medium-priority items can be scheduled for the next quarter. Low-priority gaps are addressed during routine maintenance cycles. Involve stakeholders from IT, compliance, legal, and business leadership to ensure the prioritization reflects both technical severity and business context.
6. Build and Execute a Remediation Roadmap
Translate prioritized findings into a phased action plan. Each remediation item should have a specific task description, an assigned owner, a deadline, required resources or budget, and a success metric. Phase 1 addresses high-risk gaps, Phase 2 tackles medium-risk items, and Phase 3 covers low-risk improvements and ongoing hardening.
A strong remediation roadmap considers not only the technical fix but also the budget implications, staffing requirements, and compliance deadlines. Track progress using measurable KPIs: control maturity scores, percentage of high-risk gaps closed, mean time to remediate, and overall exposure reduction.
7. Reassess and Establish a Continuous Improvement Cycle
A gap analysis is not a one-time event-it is the starting point of a repeatable improvement cycle. Schedule comprehensive reassessments at least annually, and trigger additional reviews after significant events such as cloud migrations, mergers, regulatory changes, or security incidents.
Integrate gap analysis findings into your broader security operations: feed them into vulnerability management workflows, incorporate them into secure architecture reviews, and reference them in incident postmortems. If the same weakness appears in multiple review cycles, the problem is systemic - address the root cause rather than patching the symptom repeatedly. Over time, this cycle builds defense-in-depth and transforms security improvement from an ad-hoc activity into a measurable, accountable program.
Most Common Security Gaps Organizations Discover
Across industries and organization sizes, certain gaps surface repeatedly. Awareness of these patterns helps you know where to look first.
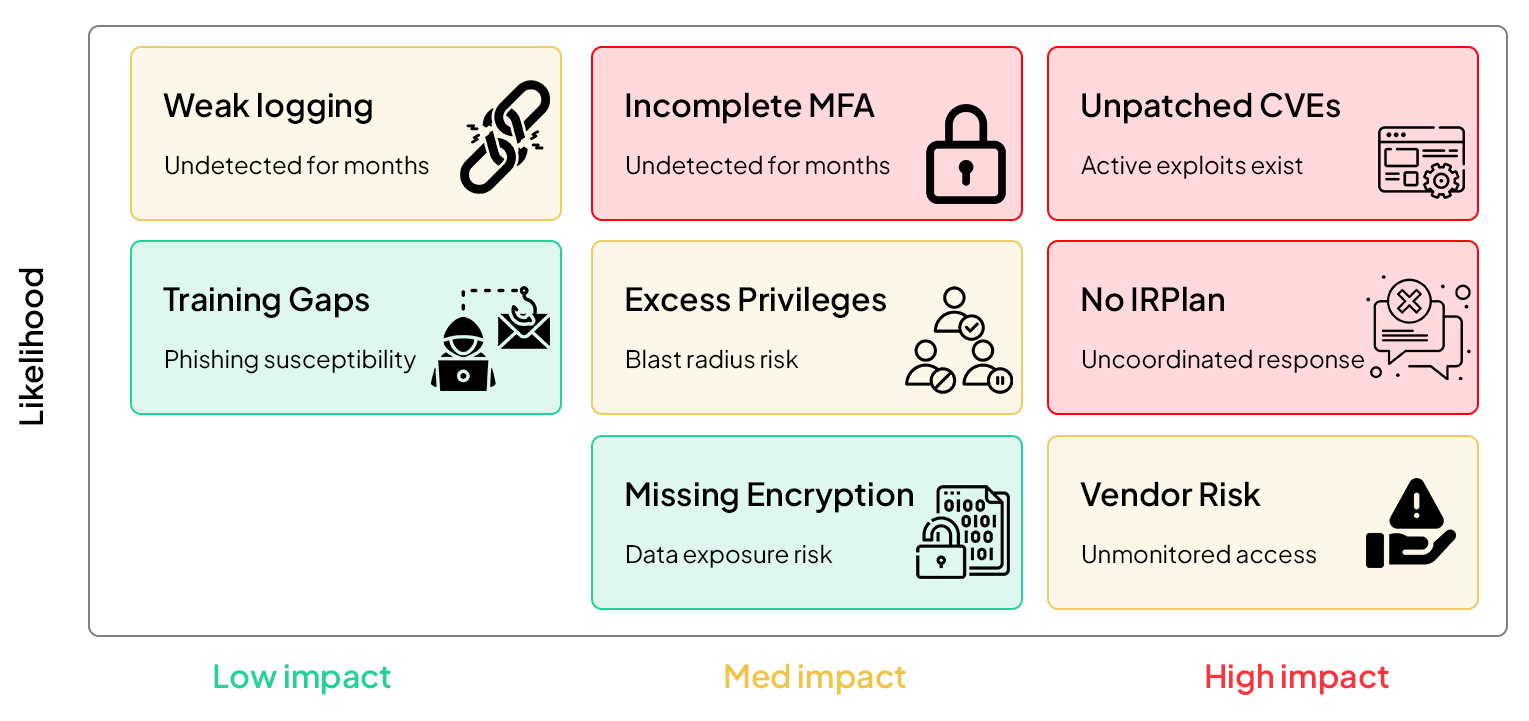

Pro tip: Pay close attention to gaps that interact with each other. An inconsistent patching practice might seem moderate on its own, but when combined with an unmonitored remote access tool, it becomes a critical exposure. The best gap analyses evaluate systemic risk - not just individual findings in isolation.
Tools and Approaches That Accelerate Gap Analysis
While a gap analysis can be performed with spreadsheets and manual reviews, the right tools dramatically improve speed, accuracy, and repeatability. Here are the categories of tools professionals rely on:
GRC Platforms provide centralized dashboards for mapping controls to frameworks, tracking remediation, and generating audit-ready reports. They are especially valuable for organizations managing multiple compliance frameworks simultaneously.
Vulnerability Scanners automate the detection of missing patches, misconfigurations, and known technical weaknesses. They provide the raw technical data that feeds into the broader gap analysis. Run these regularly-not just during formal assessments.
Penetration Testing validates whether identified gaps are actually exploitable under real-world conditions. Automated scanning finds potential weaknesses; penetration testing proves which ones can be leveraged by an attacker to achieve meaningful impact.
Cloud Security Posture Management (CSPM) tools continuously monitor cloud configurations against best practices (such as the AWS Well-Architected Security Pillar or CIS Benchmarks for Azure and GCP). Given how rapidly cloud environments change, manual reviews alone cannot keep pace.
SIEM and Detection Engineering analysis is often overlooked but critical. Reviewing alert quality, use-case coverage, and log retention during a gap analysis ensures that your detection capabilities are genuinely effective-not just generating noise.

FAQs
Q1. What is a security controls gap analysis?
A security controls gap analysis is a structured assessment that compares your organization's current security controls, policies, and processes against a desired target state-such as NIST CSF, ISO 27001, or CIS Controls. It identifies where controls are missing, weak, or misconfigured and produces a prioritized remediation plan to close those gaps. Unlike a vulnerability scan, which focuses on technical flaws, a gap analysis evaluates people, processes, and technology holistically.
Q2. How often should we perform a security controls gap analysis?
Organizations should perform a comprehensive gap analysis at least once per year. Additional assessments should be triggered after major changes-cloud migrations, mergers or acquisitions, new regulatory requirements, significant staffing changes, or security incidents. Continuous monitoring tools can supplement annual reviews by flagging emerging gaps in real time, but they do not replace the depth of a formal periodic assessment.
Q3. What is the difference between a gap analysis and a vulnerability scan?
A vulnerability scan is a narrow, automated technical tool that detects known system weaknesses like missing patches or misconfigurations. A gap analysis is a broad strategic assessment that evaluates policies, processes, access controls, governance practices, and organizational readiness against a compliance framework. A vulnerability scan is one input within a gap analysis, but a gap analysis delivers the full strategic roadmap that a scan alone cannot provide.
Q4. What is the difference between a gap analysis and a risk assessment?
A gap analysis measures the distance between your current controls and a defined standard, identifying what is missing. A risk assessment evaluates threats and vulnerabilities to determine the probability and business impact of potential security incidents. They answer different questions but are most powerful when used together: the gap analysis tells you what you lack, and the risk assessment tells you which gaps pose the greatest threat.
Q5. Which frameworks are commonly used as benchmarks?
The most widely adopted frameworks include NIST Cybersecurity Framework (CSF 2.0), ISO/IEC 27001 and 27002, CIS Controls v8, HIPAA for healthcare, PCI DSS for payment card data, SOC 2 Trust Services Criteria for SaaS providers, and CMMC for defense contractors. The choice depends on your industry, regulatory obligations, customer requirements, and current security maturity level.
Q6. Can small businesses benefit from a gap analysis?
Yes-often more than large enterprises. Small businesses are frequently targeted by attackers precisely because their security controls tend to be less mature. A gap analysis helps smaller organizations focus limited budgets on the controls that reduce the most risk, rather than spreading resources thinly across every possible security measure. It provides a phased roadmap that matches the organization's capacity to execute.
Q7. How long does a security controls gap analysis take?
For small to mid-sized organizations, a thorough gap analysis typically takes one to three weeks. Larger enterprises with complex multi-cloud environments, numerous business units, and multiple regulatory obligations may require four to eight weeks. Automated GRC and CSPM platforms can significantly accelerate the data-gathering and mapping phases, but the analysis, prioritization, and roadmap development still require experienced human judgment.
Q8. What are the most common security gaps organizations find?
The most frequently discovered gaps include incomplete multi-factor authentication deployment, outdated or unpatched software, excessive user privileges that violate least-privilege principles, weak or untested incident response plans, insufficient logging and monitoring, missing data encryption for sensitive information, unmanaged third-party vendor risk, and lack of regular security awareness training. Many of these gaps are process-oriented rather than purely technical, which is why automated scanning alone is insufficient.
Get Notified
BLOGS AND RESOURCES