Introduction:
On April 15, 2026, the National Institute of Standards and Technology (NIST) made an announcement that quietly reshuffled the foundations of vulnerability management as we know it. The National Vulnerability Database, the world's most widely used public source of CVE enrichment data, can no longer keep up. Faced with a 263% surge in CVE submissions between 2020 and 2025, and with 2026 already outpacing last year's record, NIST has moved to a selective, risk-based enrichment model. Thousands of vulnerabilities will now enter the database without CVSS scores, without CPE mappings, and without the actionable context security teams rely on to prioritize and remediate threats.
For organizations that built their patching policies, compliance workflows, and CI/CD pipeline gates around NVD-enriched data, this is not a minor operational tweak; it is a structural break. The assumption of universal enrichment is gone. And for most security teams, the gap this creates is already wider than they realize.
At Loginsoft, we saw this coming. Our LOVI platform was built precisely for this moment to provide independent, analyst-validated vulnerability intelligence that operates entirely outside the NVD enrichment queue. In this post, we break down exactly what changed, who is affected, and how Loginsoft ensures your security program stays complete, current, and in control.
Key Takeaways
What you need to know before reading on
- NIST will now enrich only three categories of CVEs, CISA KEV, federal software, and EO 14028 critical software. Everything else is labeled "Not Scheduled," leaving thousands of vulnerabilities without CVSS scores, CPE mappings, or exploitability context.
- Security scanners, patching workflows, and compliance programs that rely on NVD enrichment are now operating with significant, silent blind spots, and most teams don't know it yet.
- Loginsoft LOVI platform delivers independent, analyst-enriched CVE intelligence regardless of NVD status, ensuring your security program never has an unenriched gap.
The Ground Just Shifted Under Vulnerability Management
For more than two decades, the National Vulnerability Database has been the bedrock of the global cybersecurity ecosystem. Security teams across industries built their patching workflows, compliance programs, and risk scoring engines on one assumption: that NIST would enrich every Common Vulnerability and Exposure (CVE) with the metadata needed to make it actionable severity scores, affected product lists, and exploitability context.
That assumption is now officially invalid.
On April 15, 2026, NIST announced a fundamental restructuring of NVD operations. Overwhelmed by a 263% surge in CVE submissions between 2020 and 2025 and with 2026 already running one-third ahead of last year's record, the agency has shifted to a selective, risk-based enrichment model. Only a small subset of vulnerabilities will receive the full treatment security teams have come to depend on. The rest will be labeled "Not Scheduled" and left without enrichment until resources allow if ever.
The downstream impact is not theoretical. It is immediate, structural, and already spreading through security programs worldwide. This blog examines exactly what changed, why it creates a critical visibility gap, and how Loginsoft's LOVI platform is designed to fill it completely, continuously, and without disruption to your workflows.
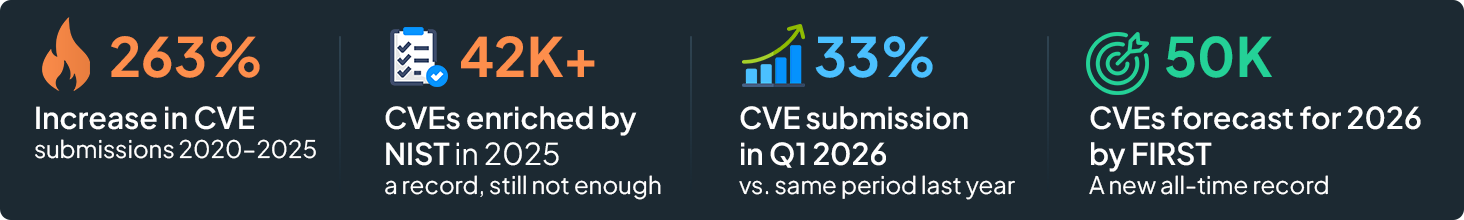
- 263% Increase in CVE submissions, 2020–2025
- 42K+ CVEs enriched by NIST in 2025 a record, still not enough
- 50K CVEs forecast for 2026 by FIRST a new all-time record
- +33% CVE submissions in Q1 2026 vs. same period last year

What Exactly Did NIST Change And What Does It Mean?
The NVD's new model is not a shutdown. NIST is still publishing CVEs, maintaining the database, and enriching a defined subset of vulnerabilities. What has changed is the default expectation: universal enrichment is gone.
Under the previous model, every CVE submitted to the NVD was analyzed, scored with CVSS severity ratings, mapped to affected software using Common Platform Enumeration (CPE) identifiers, and cross-referenced for completeness even when the submitting CVE Numbering Authority (CNA) had already provided a score. That redundancy was a feature, not a bug. It provided a trusted, independent cross-check.
Going forward, enrichment is reserved for three priority categories:

A further reduction that has not received enough attention: NIST has stopped providing its own independent CVSS score when submitting CNA has already provided one. For years, this dual-scoring served as a quality check. CNA-provided data varies significantly in rigor and depth. Removing the cross-check means organizations are now accepting vendor-provided severity ratings at face value a risky posture in a market where vendors have inherent incentives to under-score their own vulnerabilities.
The Real-World Impact on Security and Development Teams
The consequences of this shift are not abstract. They break specific, well-established workflows across security and engineering organizations.
Security Teams
Patching policies built on CVSS thresholds become unreliable when scores are missing or unvalidated. Compliance programs dependent on NVD data for audit evidence face gaps. Vulnerability scanners that ingest NVD feeds will silently flag fewer issues - not because the environment is safer, but because enrichment data is absent. Security leaders must reassess tool dependencies immediately.
Development & DevSecOps Teams
CI/CD pipelines that gate deployments on vulnerability severity can no longer trust that all detected issues have been scored. Without prescriptive metadata, teams lose the signal they need to differentiate between blocking issues and acceptable technical debt. Innovation velocity suffers when developers are forced to manually evaluate unenriched vulnerabilities.
Compliance & GRC Programs
Frameworks like FedRAMP, SOC 2, ISO 27001, and PCI-DSS reference NVD-enriched data for risk scoring and remediation of SLAs. When enrichment is absent, auditors and risk officers face unanswerable questions about the severity of known vulnerabilities - creating liability and compliance uncertainty.
Global Private-Sector Organizations
The new enrichment criteria heavily favor the U.S. federal government supply chain. Private-sector enterprises, European organizations, SaaS vendors, and commercial software teams operating outside the federal ecosystem will receive the least coverage under the new model - yet face identical threat landscapes.

How Loginsoft's LOVI Platform Solves the Enrichment Gap
The crisis created by NIST's policy shift is real but it is entirely solvable for organizations that do not rely on the NVD as their sole enrichment source. This is precisely the problem Loginsoft built LOVI to address.
LOVI (Loginsoft Open Vulnerability Intelligence) is an independent vulnerability research and intelligence platform that enriches CVE data through a combination of expert analyst work, multi-source aggregation, and validated scoring operating completely outside the NVD enrichment pipeline. Whether a CVE is "Priority" or "Not Scheduled" in NIST's model is irrelevant to LOVI's coverage. Every disclosed vulnerability is analyzed on its own merits.
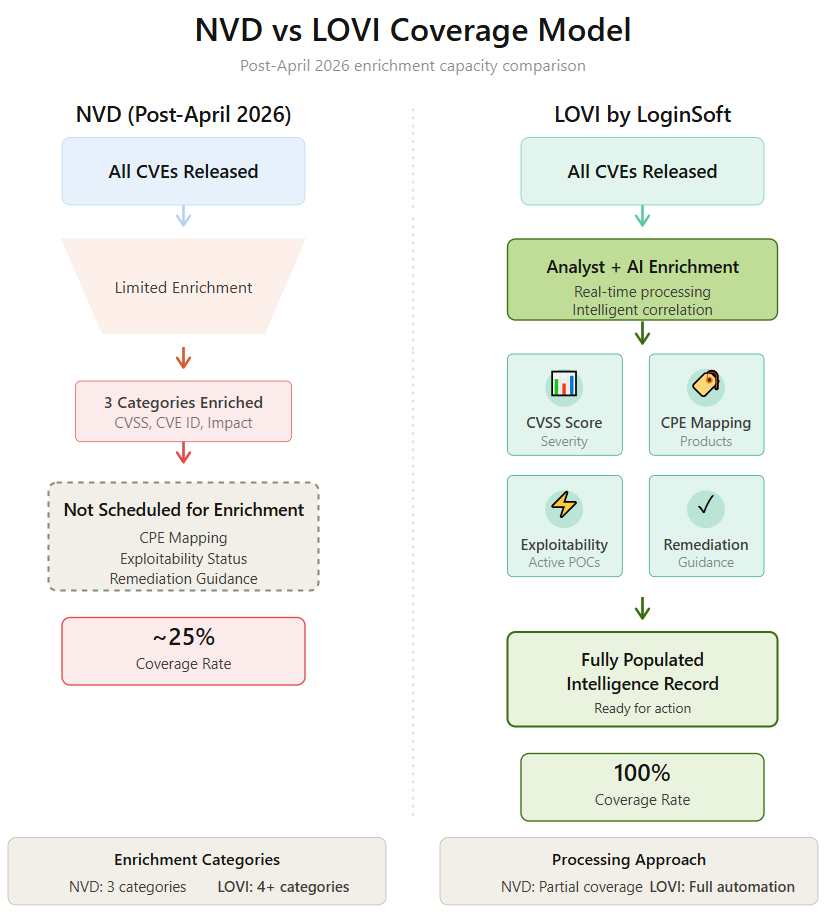
Independent Analyst Enrichment No NVD Dependency
Loginsoft vulnerability research team monitors CVE disclosures across all CNA sources, independently validates severity scores, and produces enrichment records without waiting on NVD queues. CVEs labeled "Not Scheduled" by NIST are treated as first-class research targets, not as backlogs. Your teams get actionable data regardless of NVD status.
Rapid Disclosure Coverage with Validated CVSS Scoring
LOVI does not simply relay CNA-provided scores. Every severity assessment is independently cross-checked and validated against technical evidence, vendor advisories, and exploit data. Because NIST has eliminated its own CVSS cross-check for CNA-supplied scores, LOVI now fills out a critical quality assurance role that the NVD has abdicated.
Precise CPE Mapping and False-Positive Elimination
NVD records have historically mapped vulnerabilities broadly across entire product lines, causing scanners to flag versions that are not actually affected. LOVI's enrichment process validates the exact component versions impacted - reducing false-positive noise and ensuring developers are not chasing phantom vulnerabilities that waste sprint cycles.
Actionable Remediation Guidance Not Just Raw Data
Every LOVI advisory includes specific remediation steps: exact fixed versions, patch availability timelines, and workarounds when patches are not yet available. Security teams and developers receive the context to act, not just the signal to worry. This is especially critical for zero-day events where NVD enrichment may lag by days or weeks.
How LOVI Enriches a CVE From Disclosure to Actionable Intelligence
- CVE Disclosed by CNA or Researcher
- LOVI Ingestion & Multi-Source Cross-Reference
- Analyst Validation & Independent CVSS Scoring
- Exploit & Exploitability Context Added
- Remediation Guidance Published to LOVI Platform

Why Loginsoft - and Why Now
Loginsoft is not a newcomer responding opportunistically to a crisis. The organization has been building vulnerability research capabilities and open-source security intelligence for years, working at the intersection of software supply chain security, CVE research, and threat intelligence. LOVI is the operationalized expression of that research depth - purpose-built for teams that need more than a government database that can sustainably provide.
What makes this moment particularly urgent is the convergence of two accelerating trends. First, AI-assisted vulnerability discovery is compressing the time between a software flaw's existence and its formal CVE disclosure. More vulnerabilities are being found, documented, and weaponized faster than any manual enrichment system can process them. Second, AI-assisted attack tooling is lowering the barrier for adversaries to exploit newly disclosed vulnerabilities - often before enriching data even enters the NVD pipeline.
The result is a closing window. Organizations that wait for NVD enrichment before acting on a vulnerability are operating on a timeline that increasingly serves attackers, not defenders. LOVI closes that window by delivering enriched intelligence on the timescale that modern threats demand.
The Strategic Case for Independent Vulnerability Intelligence
The NIST announcement is not a temporary setback. CVE volume will not decline. The structural pressures driving the NVD's pivot exponential disclosure growth, AI-augmented discovery, global proliferation of CVE Numbering Authorities are permanent features of the vulnerability landscape. This means the gap between CVE disclosure and NVD enrichment will continue to widen, not narrow.
Organizations that treat this as a one-time disruption to weather will find themselves repeatedly exposed. Those that use this moment to establish an independent, high-fidelity vulnerability intelligence capability will build a durable competitive advantage in cyber resilience. Loginsoft LOVI platform is designed to be that capability not a stopgap, but a long-term intelligence foundation.
What Your Security Team Should Do Right Now
If you have not yet assessed how the NVD policy change affects your organization, here are the five immediate action steps security leaders should take:
- Audit your NVD dependency
Identify every tool, workflow, and policy that ingests NVD-enriched data. This includes vulnerability scanners, SIEM integrations, ticketing system triggers, and compliance reporting pipelines. - Identify your "Not Scheduled" exposure
Review your current vulnerability inventory for CVEs that were awaiting enrichment as of March 1, 2026. These have now been reclassified and may lack the metadata your tools need. - Evaluate CNA-provided severity scores critically
With NIST's independent CVSS cross-check removed, treat vendor-supplied scores as one data point not the final word. Build processes for validating severity against independent sources. - Establish a supplemental intelligence source
Do not operate with a single point of failure in your vulnerability enrichment pipeline. LOVI by Loginsoft provides the independent enrichment coverage your existing tools now lack. - Update patching and escalation policies
Policies based on "all CVEs will have a CVSS score" are no longer valid. Revise your thresholds and escalation triggers to account for partially or unenriched vulnerabilities.
FAQs
Q1. What exactly changed in NIST's NVD policy in April 2026?
Starting April 15, 2026, NIST shifted from enriching all CVEs to a selective risk-based model. Only CVEs in the CISA KEV catalog, those affecting U.S. federal government software, and those meeting EO 14028 critical software definitions receive automatic NVD enrichment. All other CVEs are published to the database with the status "Not Scheduled" meaning no CVSS scores, CPE mappings, or technical analysis from NIST unless specifically requested.
Q2. How many CVEs will be left unenriched under the new NVD model?
The vast majority of newly submitted CVEs potentially tens of thousands per year will lack NVD enrichment data by default. FIRST forecast 50,000 CVE disclosures for 2026 alone. With NIST enriching only a narrow federal-focused subset, most commercial, open-source, and private-sector vulnerabilities will enter the database unenriched. Additionally, all pre-March 2026 backlogged CVEs have already been reclassified as "Not Scheduled."
Q3. Will my existing vulnerability scanner still work after the NVD changes?
Scanners that rely exclusively on NVD-supplied CVSS scores and CPE data will develop significant blind spots. Tools will report vulnerabilities as lower risk or fail to flag them entirely when enrichment data is absent. This creates a false sense of security. Organizations need a supplemental intelligence source, like Loginsoft LOVI platform, to maintain complete and accurate vulnerability visibility.
Q4. What is LOVI and how does it solve the NVD enrichment gap?
LOVI (Loginsoft Open Vulnerability Intelligence) is Loginsoft's vulnerability research and intelligence platform. It provides analyst-enriched CVE data including independent CVSS scoring, CPE mapping, exploitability context, and remediation guidance completely independent of NVD enrichment status. LOVI covers CVEs regardless of whether NIST has labeled them "Scheduled" or "Not Scheduled," ensuring organizations have the actionable data they need to prioritize and remediate effectively. Visit lovi.loginsoft.com to learn more.
Q5. How does Loginsoft keep CVE enrichment current and accurate?
Loginsoft's research team continuously monitors CVE disclosures across all CNA and researcher sources, cross-references multiple intelligence feeds, validates severity scores against technical evidence, and publishes enriched advisories to the LOVI platform. The process includes independent CVSS scoring, exact CPE version validation to eliminate false positives, exploit availability tracking, and specific remediation guidance all with rapid turnaround timed to the disclosure event, not the NVD queue.
Q6. Which organizations are most at risk from the NVD 2026 policy change?
Any organization that depends on NVD-enriched data for patching prioritization, compliance auditing, or CI/CD pipeline gating is affected. This is especially acute for private-sector enterprises, SaaS companies, open-source software consumers, and global organizations outside the U.S. federal government supply chain since the new enrichment criteria heavily favor federal-use software. Organizations in financial services, healthcare, technology, and critical infrastructure with mature vulnerability management programs should treat this as a Tier 1 operational risk.
Q7. Can organizations request enrichment from NIST for "Not Scheduled" CVEs?
Yes, NIST has provided an email address (nvd@nist.gov) for organizations to request enrichment of specific unenriched CVEs. However, NIST will review requests and schedule enrichment "as resources allow," with no guaranteed timeline. For security teams that need timely, reliable enrichment for operational decision-making, this manual request process is not a scalable substitute for independent vulnerability intelligence coverage.
Q8. Is the NVD being shut down?
No. The NVD is not shutting down. NIST continues to publish all submitted CVEs and maintains the database infrastructure. The change is specifically about the depth and timeliness of enrichment data added to each CVE record. The database remains a foundational reference - but it can no longer serve as the primary, reliable source of enriched vulnerability context for organizations with comprehensive security requirements.
Get Notified
BLOGS AND RESOURCES













